Trezor Login: The Ultimate Guide to Secure Your Crypto Journey
Master the Trezor Login process and take full control of your digital assets safely.
🔒 What Is Trezor Login?
Trezor Login is the secure gateway that connects you to your Trezor hardware wallet — the trusted cold storage solution for managing cryptocurrencies offline. With Trezor, users can store, send, and receive coins like Bitcoin, Ethereum, and thousands of other tokens without relying on centralized exchanges or vulnerable online systems.
By using Trezor Login, you’re not just accessing a wallet — you’re establishing a direct, encrypted communication with your hardware device, ensuring complete ownership of your private keys.
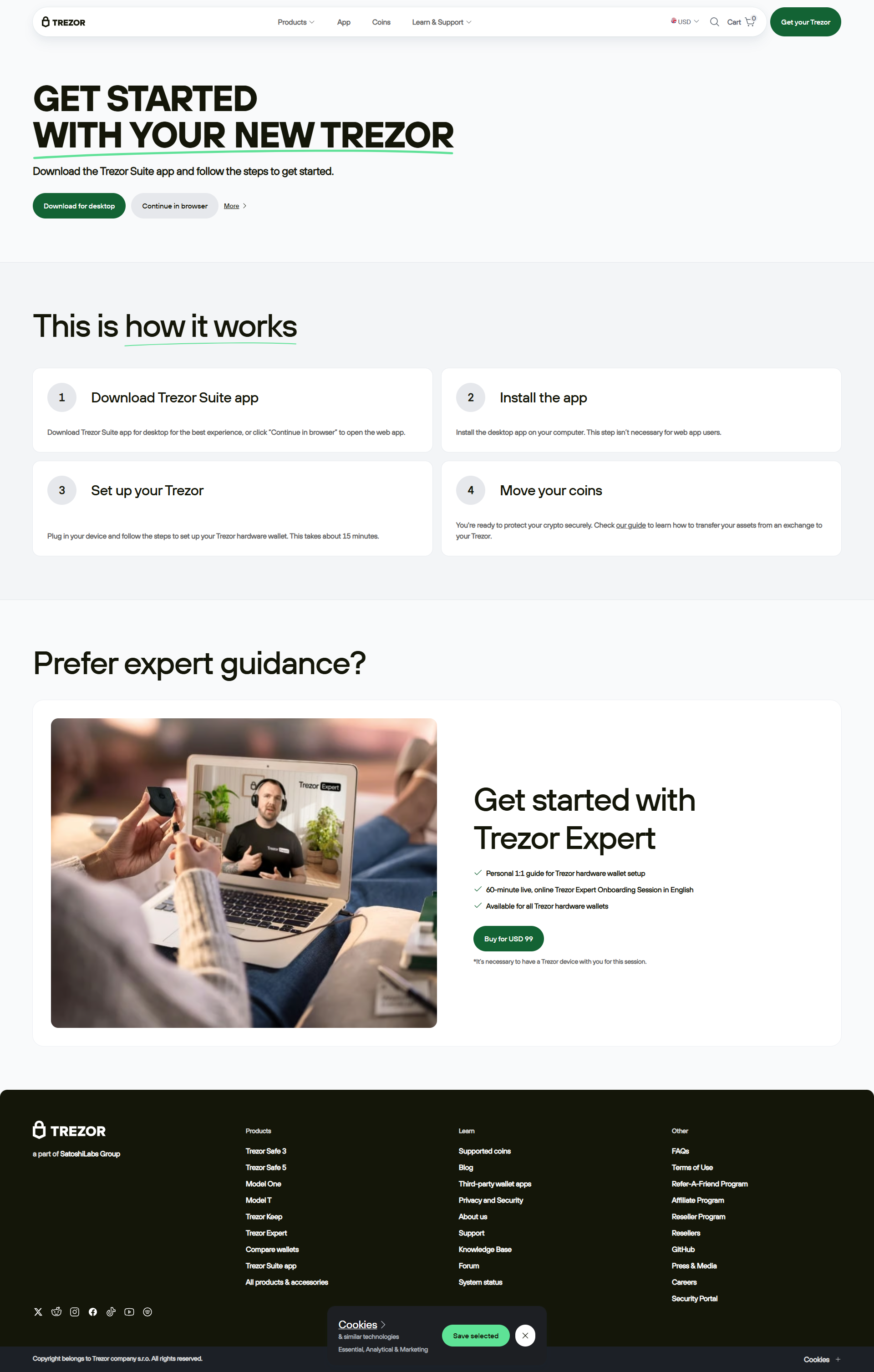
🚀 How to Access Your Trezor Wallet via Trezor Login
Let’s break down the simple and secure process to get started with Trezor Login:
Step 1: Visit Trezor.io
Go to the official Trezor.io website. Never use third-party links to avoid phishing risks.
Step 2: Open Trezor Suite
Click “Access Suite” to open the Trezor Suite — the desktop or web interface for managing your assets.
Step 3: Connect Your Device
Plug in your Trezor Model T or Trezor One using a USB cable and wait for it to sync securely.
Step 4: Enter PIN
Authenticate using your unique PIN code directly on the device — no keyboard inputs mean no keyloggers.
Step 5: Access Dashboard
Once verified, your Trezor dashboard loads instantly — view balances, send coins, and manage tokens effortlessly.
🧠 Why Use Trezor Login?
Unlike web wallets or exchange accounts, Trezor Login ensures that your private keys never leave your hardware device. This means no hacker, malware, or data breach can compromise your assets unless they have your physical Trezor device and PIN.
Here are some standout benefits:
- ✔️ Cold storage for ultimate protection
- ✔️ Direct control of private keys
- ✔️ User-friendly interface with Trezor Suite
- ✔️ Open-source and community-trusted software
- ✔️ Multi-asset support (Bitcoin, Ethereum, and more)
💡 Trezor Login vs Other Wallets
| Feature | Trezor Login | Exchange Wallets | Software Wallets |
|---|---|---|---|
| Private Key Storage | On Hardware (Offline) | On Exchange Server | On Device (Online) |
| Security Level | Very High | Low | Medium |
| Ease of Use | High (via Suite) | High | Medium |
| Phishing Resistance | Excellent | Poor | Moderate |
💬 Pro Tip:
Always double-check the browser URL when accessing Trezor Suite online. The official domain is trezor.io. Avoid entering your recovery seed on any website — it should only be used directly on the Trezor device.
📘 Frequently Asked Questions (FAQ)
1. Can I access Trezor Login from mobile?
Currently, Trezor Suite is primarily optimized for desktop use, though mobile integrations are being developed. You can manage your assets on desktop browsers or via the Trezor Suite app.
2. What if I forget my Trezor PIN?
If you forget your PIN, you’ll need to reset your Trezor device using the recovery seed. This ensures that only you can regain access, keeping others locked out.
3. Is Trezor Login safe on public Wi-Fi?
Yes, because all cryptographic operations happen inside the hardware wallet itself. However, avoid logging in from compromised or shared computers to minimize risks.
4. Can I use Trezor Login for DeFi?
Absolutely! Trezor supports DeFi platforms via integrations with wallets like MetaMask, allowing you to approve transactions securely while your keys stay offline.
Final Thoughts: Trezor Login Is Your Key to True Crypto Ownership
Using Trezor Login empowers you to safeguard your digital wealth in the most secure way possible. By leveraging offline storage and encrypted access through the Trezor Suite, you can confidently manage, store, and grow your crypto portfolio — all while maintaining full control of your private keys.
Start your secure crypto journey with Trezor Login today.